Will You Survive The Revelation? The Truth About System Interface Diagrams Exposed! - System design is more important than you think
If you are looking for Unveiling Reality: The Journey from Simulation Theory to Kabbalistic you've visit to the right page. We have 35 Images about Unveiling Reality: The Journey from Simulation Theory to Kabbalistic like Exposed and vulnerable: Recent attacks highlight critical need to, Blog – Symbolism Communication and also SimpliFI: Hardware Simulation of Embedded Software Fault Attacks. Read more:
Unveiling Reality: The Journey From Simulation Theory To Kabbalistic
 the2020sperfectvision.org
the2020sperfectvision.org
Unveiling Reality: The Journey from Simulation Theory to Kabbalistic ...
Exposed And Vulnerable: Recent Attacks Highlight Critical Need To
 www.microsoft.com
www.microsoft.com
Exposed and vulnerable: Recent attacks highlight critical need to ...
ConspiracyRevelation.Com | Not Just Another WordPress Site – The
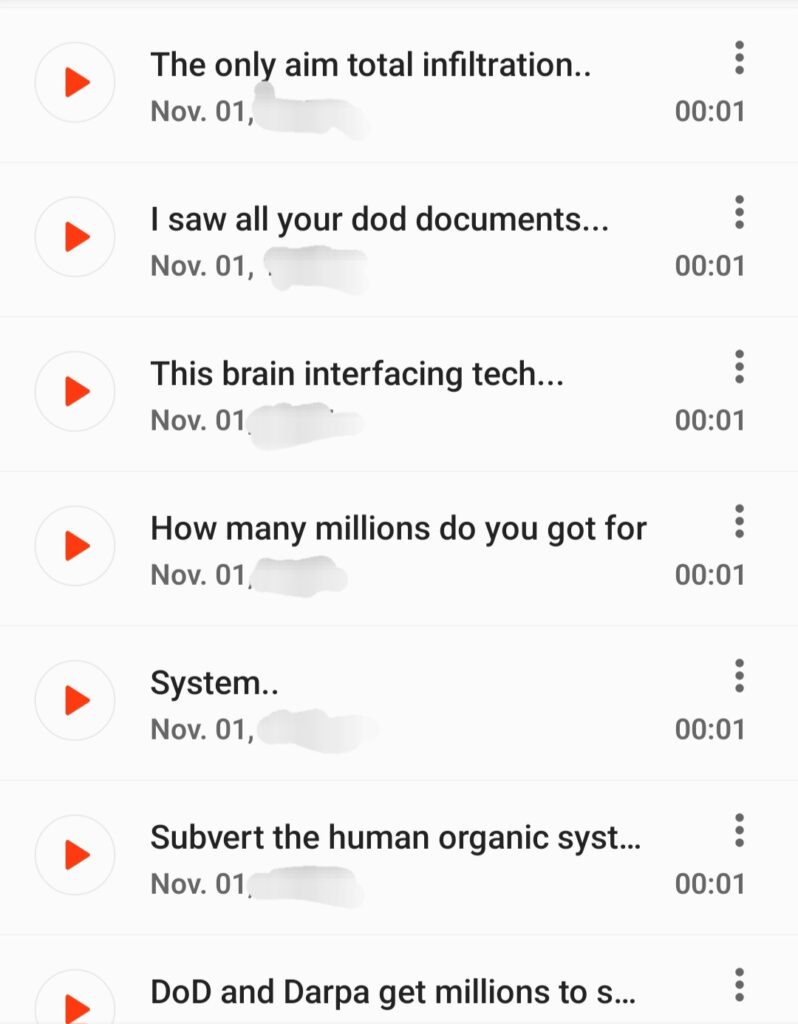 conspiracyrevelation.com
conspiracyrevelation.com
ConspiracyRevelation.Com | Not just another WordPress site – The ...
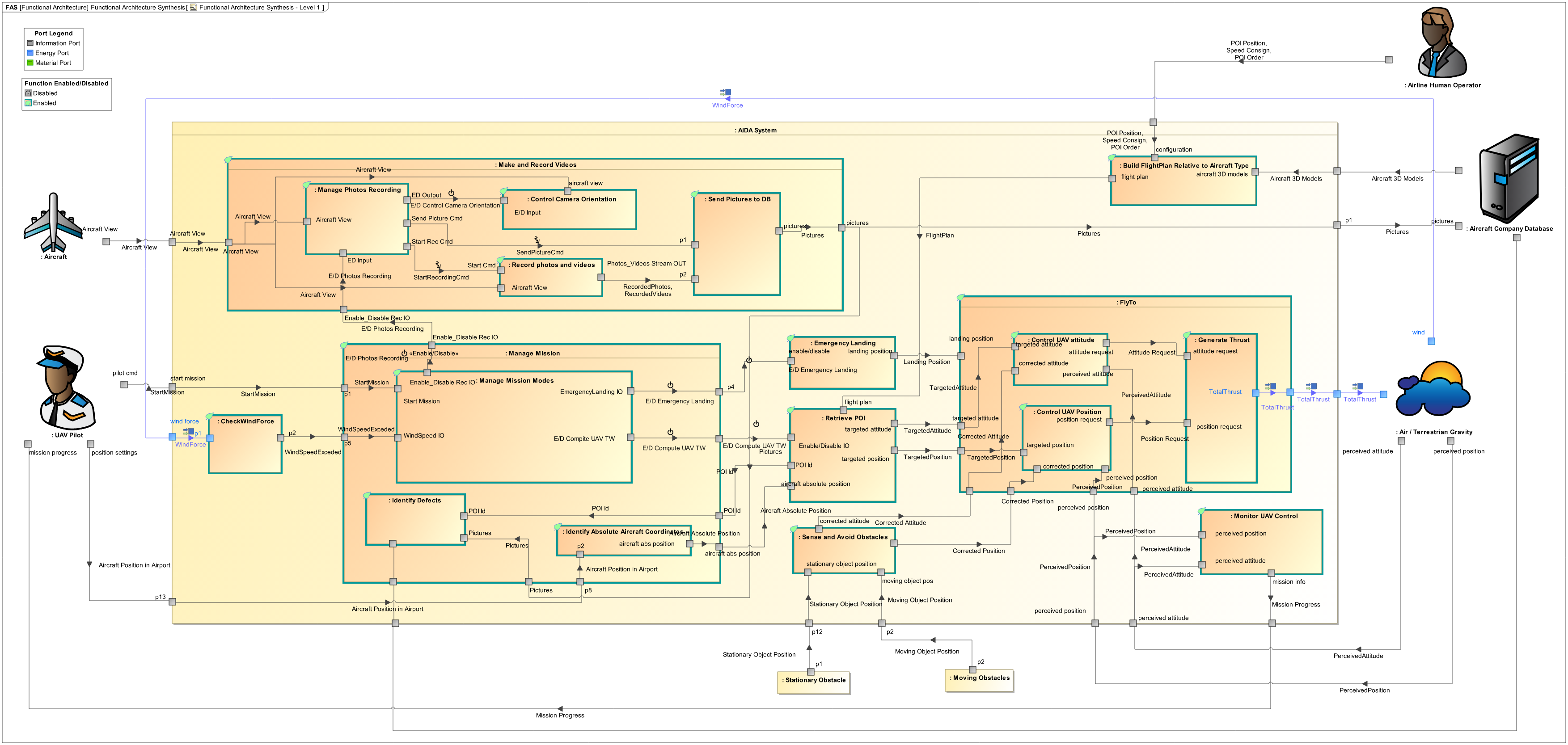
6 Myths Of Systems Engineering | PPI
 www.ppi-int.com
www.ppi-int.com
6 Myths of Systems Engineering | PPI
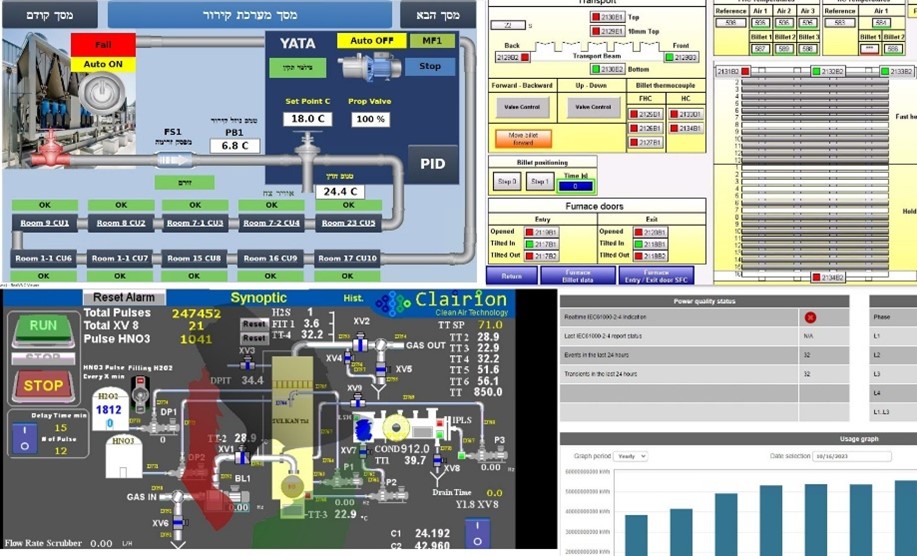
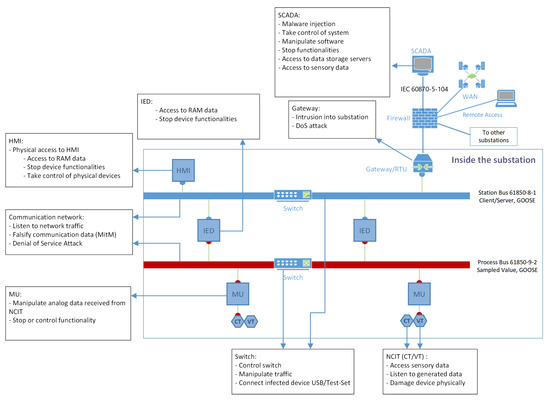
Frontiers | Consequence Simulation Of Cyber Attacks On Key Smart Grid
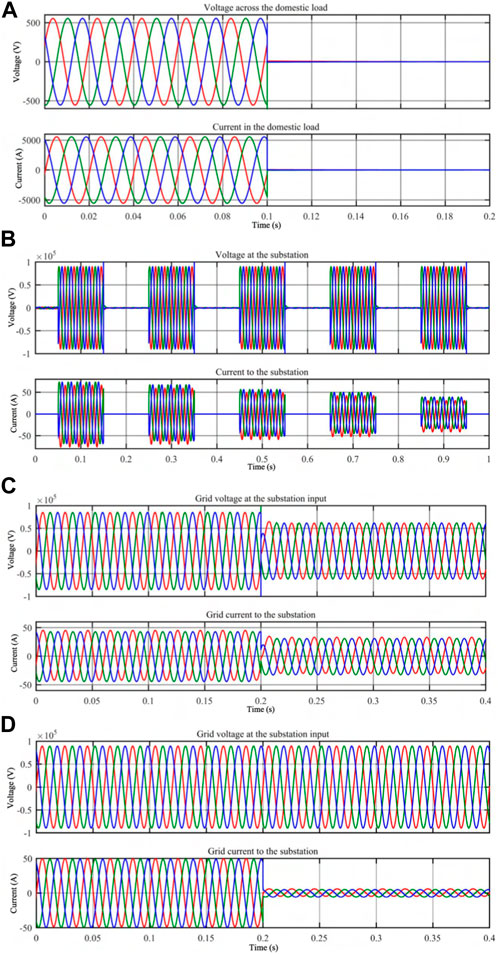 www.frontiersin.org
www.frontiersin.org
Frontiers | Consequence simulation of cyber attacks on key smart grid ...
Using VisualSim Architect For Semiconductor System Analysis | PPTX
Using VisualSim Architect for Semiconductor System Analysis | PPTX
System Interface Diagram Example At Joseph Eason Blog
 storage.googleapis.com
storage.googleapis.com
System Interface Diagram Example at Joseph Eason blog
Tell Us All Your Tech Problems
 lifehacker.com
lifehacker.com
Tell Us All Your Tech Problems
Analysis Of Electromagnetic Information Leakage Based On Cryptographic
 www.mdpi.com
www.mdpi.com
Analysis of Electromagnetic Information Leakage Based on Cryptographic ...
The REVEAL THIS System Architecture These More Complex Modules Are
 www.researchgate.net
www.researchgate.net
The REVEAL THIS system architecture These more complex modules are ...
WikiLeaks: The CIA Can Remotely Hack Into Computers That Aren't Even
 qz.com
qz.com
WikiLeaks: The CIA can remotely hack into computers that aren't even ...
WINDOW IN THE MATRIX 👁️ | 🙏Thanks To All The People Who Read Our Book
 www.instagram.com
www.instagram.com
WINDOW IN THE MATRIX 👁️ | 🙏Thanks to all the people who read our book ...
Blog – Symbolism Communication
 decodingsymbols.wordpress.com
decodingsymbols.wordpress.com
Blog – Symbolism Communication
System Design Is More Important Than You Think - DEV Community
 dev.to
dev.to
System Design is More Important Than You Think - DEV Community
Widespread Windows And Linux Vulnerabilities Could Let Attackers Sneak
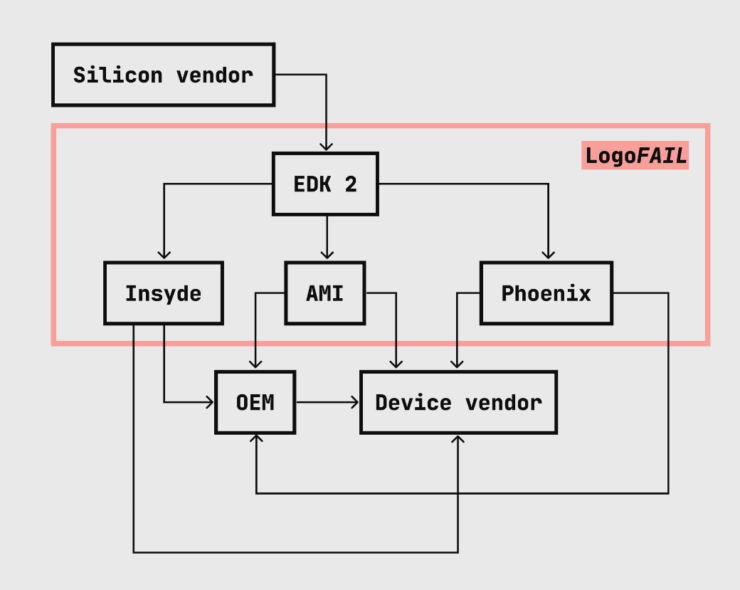 www.techrepublic.com
www.techrepublic.com
Widespread Windows and Linux Vulnerabilities Could Let Attackers Sneak ...
We Are Watching Prophecy Unfold As The Beast System Rises
 mycharisma.com
mycharisma.com
We Are Watching Prophecy Unfold as the Beast System Rises
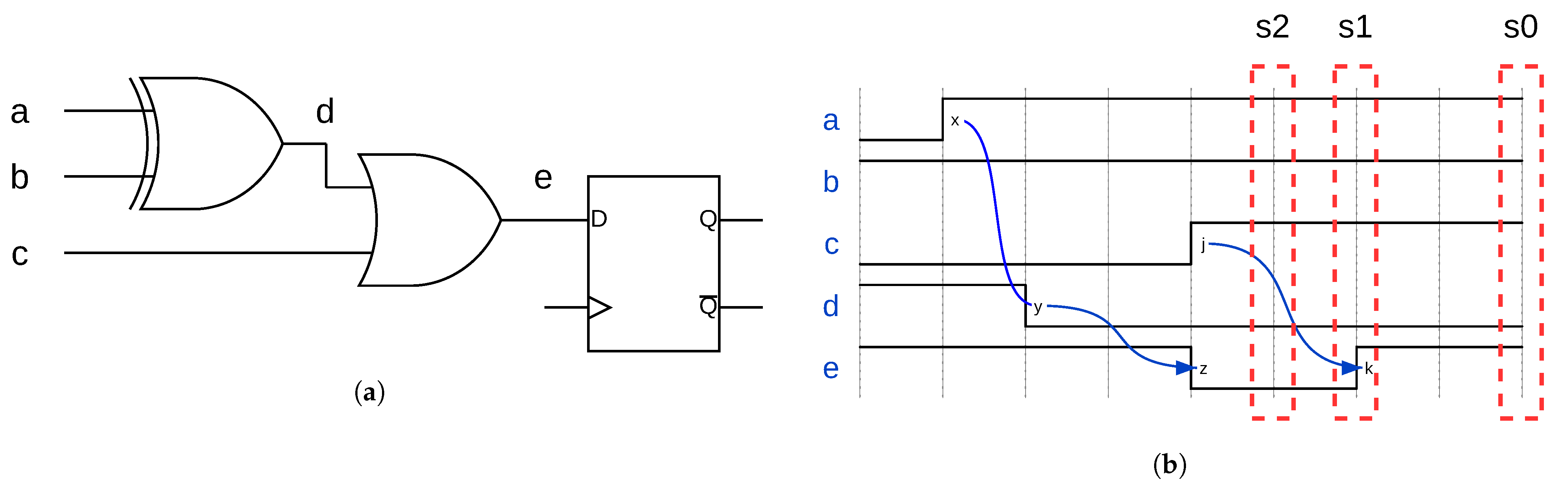
A Hardware Trojan-Detection Technique Based On Suspicious Circuit Block
 www.mdpi.com
www.mdpi.com
A Hardware Trojan-Detection Technique Based on Suspicious Circuit Block ...
ConspiracyRevelation.Com | Not Just Another WordPress Site – The
 conspiracyrevelation.com
conspiracyrevelation.com
ConspiracyRevelation.Com | Not just another WordPress site – The ...
System Interface Diagram | Download Scientific Diagram
 www.researchgate.net
www.researchgate.net
System interface diagram | Download Scientific Diagram
SimpliFI: Hardware Simulation Of Embedded Software Fault Attacks
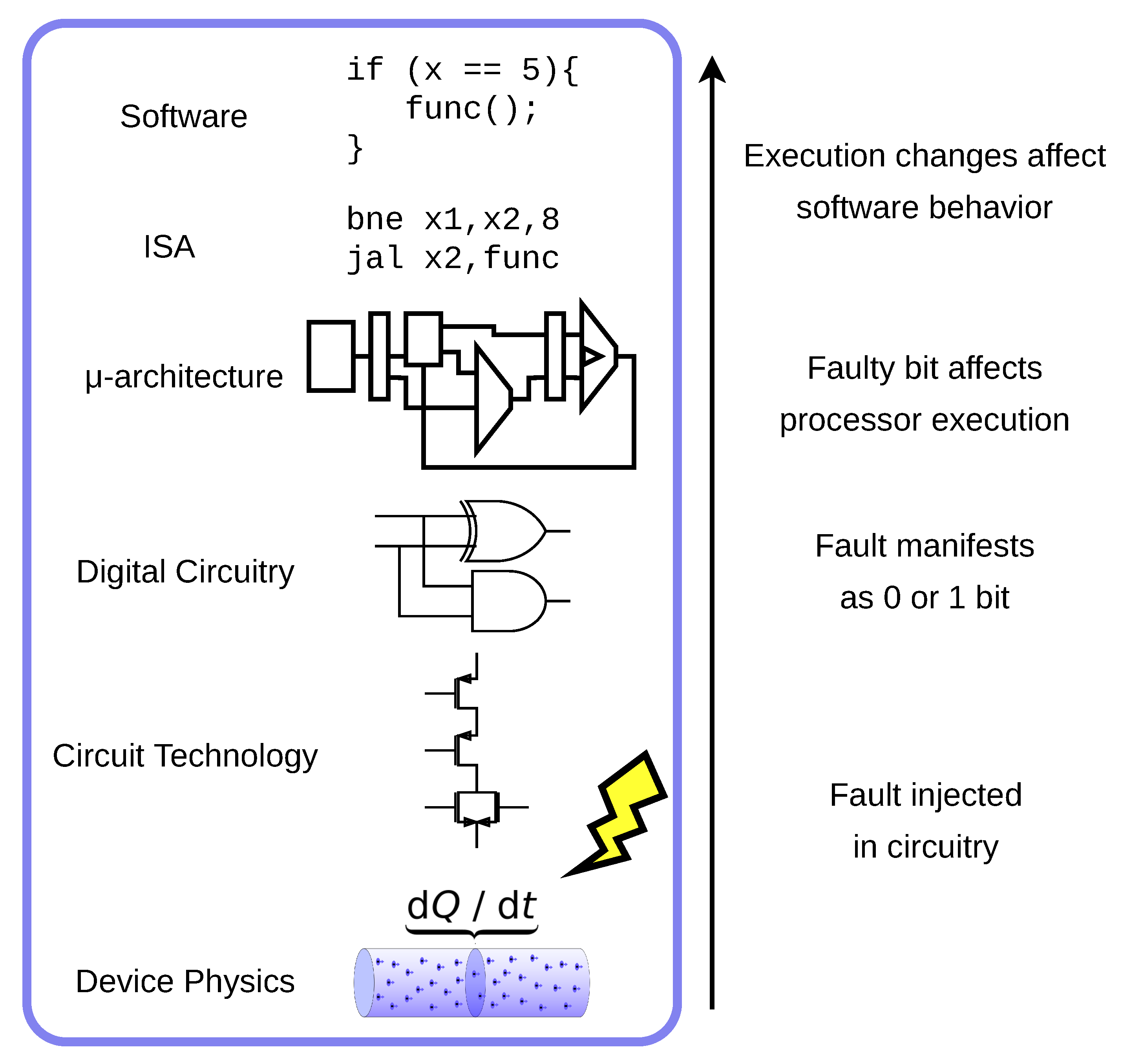 www.mdpi.com
www.mdpi.com
SimpliFI: Hardware Simulation of Embedded Software Fault Attacks
We Know Elon/Grimes Are Into Aleister Crowley. We Know Crowley Said
 www.reddit.com
www.reddit.com
We know Elon/Grimes are into Aleister Crowley. We know Crowley said ...
The Need For An Evolved Threat Intel Lifecycle | ThreatConnect
 threatconnect.com
threatconnect.com
The Need for an Evolved Threat Intel Lifecycle | ThreatConnect
User Interface Design Diagram
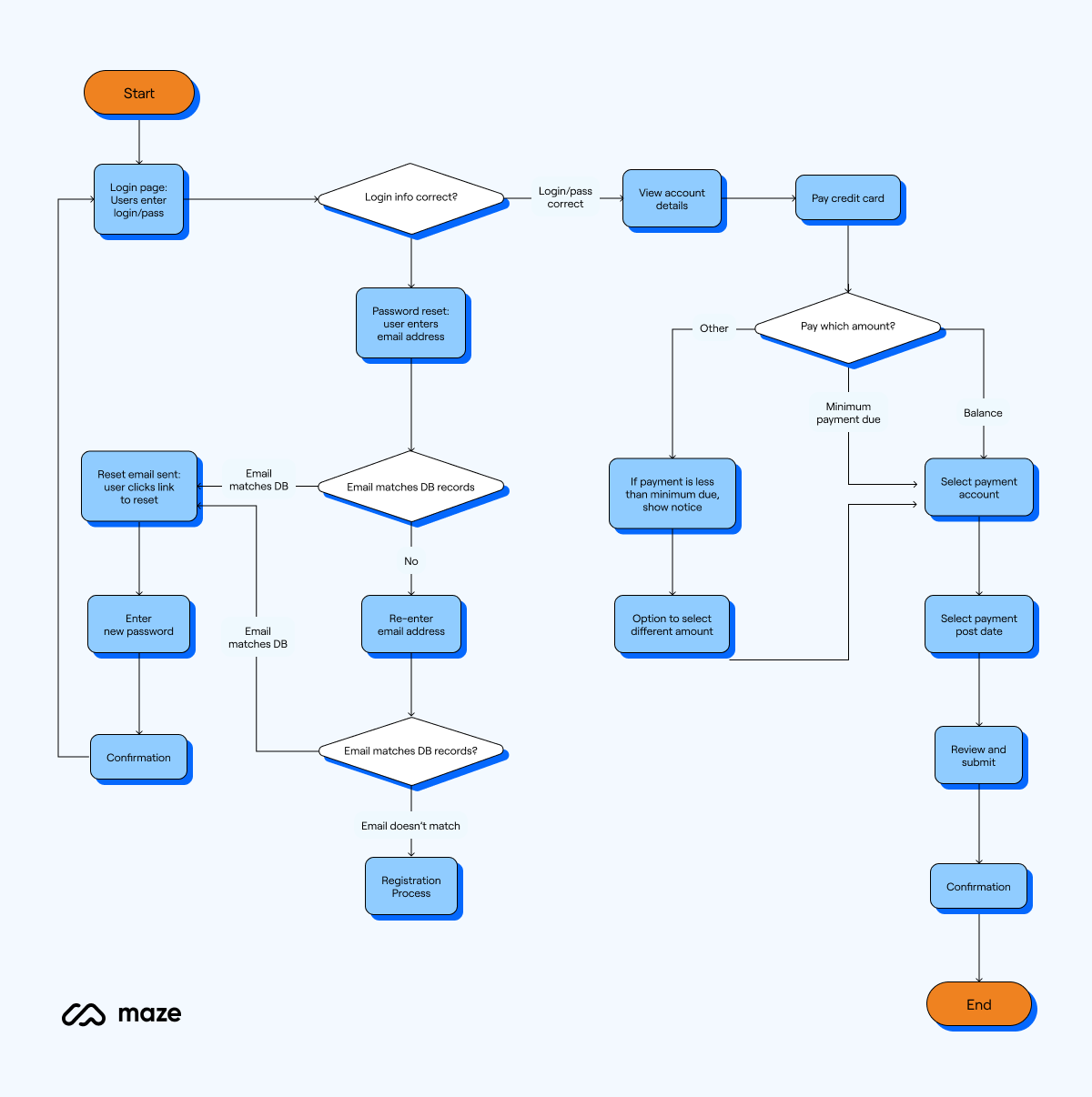 ar.inspiredpencil.com
ar.inspiredpencil.com
User Interface Design Diagram
The System Interface Showing Bits Statistics As Well As The Process Of
 www.researchgate.net
www.researchgate.net
The system interface showing bits statistics as well as the process of ...
1.2 Threats | Introduction | InformIT
 www.informit.com
www.informit.com
1.2 Threats | Introduction | InformIT
SimpliFI: Hardware Simulation Of Embedded Software Fault Attacks
 www.mdpi.com
www.mdpi.com
SimpliFI: Hardware Simulation of Embedded Software Fault Attacks
Defeat Magic With Magic: A Novel Ransomware Attack Method To
 www.mdpi.com
www.mdpi.com
Defeat Magic with Magic: A Novel Ransomware Attack Method to ...
Schematic Diagrams Of The Information Decryption Processing: A
 www.researchgate.net
www.researchgate.net
Schematic diagrams of the information decryption processing: a ...
An Approach For Analyzing Cyber Security Threats And Attacks: A Case
 www.mdpi.com
www.mdpi.com
An Approach for Analyzing Cyber Security Threats and Attacks: A Case ...
Bahas Tuntas E-KTP: Jangan Difotokopi, Micro Chip, Mind Control Dan
 kasikabar.wordpress.com
kasikabar.wordpress.com
Bahas Tuntas e-KTP: Jangan Difotokopi, Micro Chip, Mind Control dan ...
User Interface Design Diagram
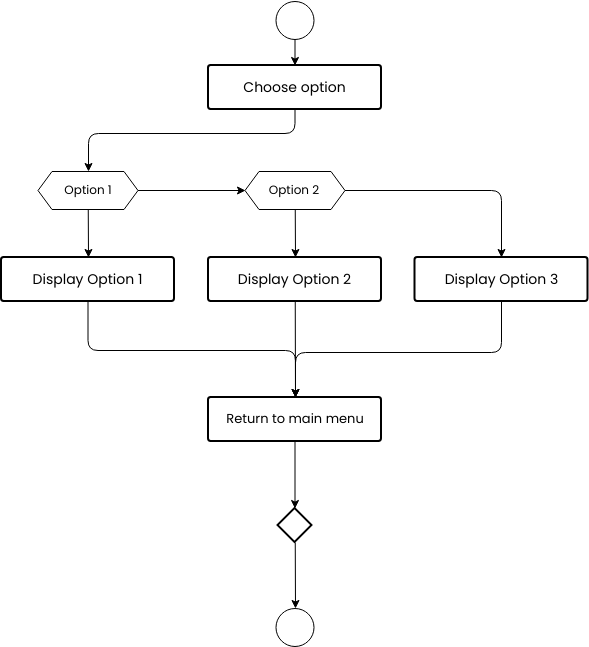 ar.inspiredpencil.com
ar.inspiredpencil.com
User Interface Design Diagram
Interface Diagram Meaning At James Glassop Blog
 storage.googleapis.com
storage.googleapis.com
Interface Diagram Meaning at James Glassop blog
Relating Maxwell’s Demon And Quantitative Analysis Of Information
 cpb.iphy.ac.cn
cpb.iphy.ac.cn
Relating Maxwell’s demon and quantitative analysis of information ...
OpManager Webcasts & Videos | How To Videos, Webinars & Solutions
 www.manageengine.com
www.manageengine.com
OpManager Webcasts & Videos | How to videos, webinars & solutions
An Architecture Of The Overall System. Messages Are Processed First
An architecture of the overall System. Messages are processed first ...
The reveal this system architecture these more complex modules are. We know elon/grimes are into aleister crowley. we know crowley said .... Relating maxwell’s demon and quantitative analysis of information ...